More 5hadowrun! I think the one big peice of the puzzle that’s now missing is a description of the matrix (the internet) and hacking checks. And to go along with that, I’ll introduce a new rogue archetype – the decker.
The Matrix
In the latest edition of Shadowrun, the internet (called the matrix because cyberpunk) has been broken, bought and taken under the control of the megacorporations. For citizens this means the matrix is much safer and more tightly controlled, and those trying to do anything illegal tend to find that their activities (and personal liberty) are shut down fairly rapidly.
 From a gameplay point of view this is great, as players can’t expect to be able to use every computer system, and even trying to communicate with their underworld contacts is difficult because everything is so closely monitored. Hence if you’re hired to steal some data from a corporation, your best bet is to physically go to their offices and find the relevant computer.
From a gameplay point of view this is great, as players can’t expect to be able to use every computer system, and even trying to communicate with their underworld contacts is difficult because everything is so closely monitored. Hence if you’re hired to steal some data from a corporation, your best bet is to physically go to their offices and find the relevant computer.
It also means that having someone on the team, like a Rogue or Rigger who can access these systems without setting off all the alarms is very useful.
Hacking
I want to keep the hacking mechanics as simple as possible. I see the whole thing as analogous to picking a lock, or disabling a trap.
- If you can find an input device (i.e. a keyboard or whatever), or you have your own terminal (tablet PC) that can connect to the system, you can make an Intelligence check to hack the system.
- If you have a Datajack and proficiency with it, you can add your proficiency bonus to the check. Rogues may gain expertise (double proficiency) with the Datajack, as they would thieves tools.
- A Datajack is a bit like an ethernet port in your head, so you still need to be physically close to the device you’re hacking into.
- What’s gained from hacking a system is up to the DM, but generally things like opening doors, disabling security systems, or deactivating defence drones would be good examples.
- Because of firewalls and other defensive measures, it’s much more difficult to hack something remote from the point of access. For example, when accessing the digital lock of a door, hacking the door open is fairly easy, while turning off alarms, accessing secure data, etc. from the same point would be difficult, if not impossible.
- Hacking into the mainframe of a system give unparalleled access, and will often be the best (or only) way of getting hold of that data you were hired to retrieve.
- As a general rule, hacking disables/deactivates security systems, rather than transferring control. Turning off the robot that’s attacking you is great, gaining it as a companion is game-breaking.
I’d suggest being quite flexible on when/if hacking checks can be repeated. For example if the players are hired to extract some data, it makes no sense for them to fail the hacking check and not be able to proceed any further; while failing to open a door just means they failed and need to find another way in. For story-critical hacks consider taking any roll as a ‘success’ but have other effects depend on the number acheived. For example a low roll might set off alarms, activate security drones, or tag the data with a tracking program. Alternatively, allow repeated attempts, with the number of attempts reflecting how bad the consequences will be; or perhaps the hacker needs to work while being attacked by security, and so repeated attempts leave them open to damage.
I’m sure proper Shadowrun players will be horrified by what I’ve suggested!
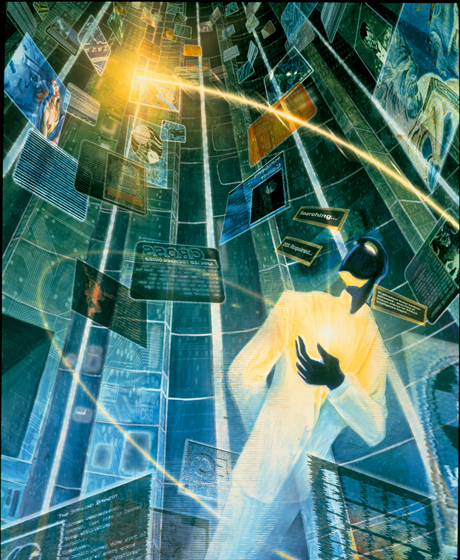
Shadowrun has a complete set of mechanics for accessing and ‘running’ the matrix, where the hack almost physically enters the system (think second life), is attacked by hostile programs, but is able to deploy companion programs to protect them.
Which is great, but it’s a whole other system that needs putting together. It also suffers from the problem that one person is doing the hacking, while the rest of the party do something else.
Now because I’ve reduced the hacking mechanics so far, I think I can get away with turning the Decker into a rogue archetype, rather than a full class.
One additional thing: I would give all rogues a Datajack and proficiency with it at level 1.
Decker

Almost all rogues are competent hackers, but a Decker can pull information out of the matrix in their sleep. Named for the large keyboard ‘decks’ that used to be their tool of choice, a skilled Decker is always in demand to act as information brokers, identity thieves, or simply private investigators.
Quick Subroutine
When you choose this archetype at 3rd level, you may use your Datajack to make a hacking attempt as a bonus action.
Information Broker
Beginning at level 3, you have advantage on all Intelligence(Investigation) checks involving the matrix (for example: searching for police records, missing persons, banking transactions, etc).
Browser History
When you reach 9th level, you may spend an hour researching a particular person to find out one piece of information about them. This research may be carried out while interacting with them, e.g. while interviewing a client or suspect. Typical information can include (others at GM discretion):
- wealth
- affiliation with groups such as corporations, political parties, etc
- home address (if listed officially)
- marital status, children, and next of kin, etc
- criminal record
I Saw a Video About This…
At 13th level, whenever you could make an Intelligence skill check (Arcana, History, Investigation, Nature, Religion or Tech), you may spend one minute researching the matrix to give yourself advantage on the roll.
You might have noticed an extra skill there: I figured in a high-tech world, it makes sense for there to be a ‘Tech’ skill, in the same way there’s Arcana and Nature. Maybe if there’s too many skills now, we can get rid of Religion? (controversial!)
Ctrl+Alt+Del
By 17th level you know how to disable simple security devices and drones quickly and quietly. If you are within 5 feet of a non-organic creature (drone, droid, turret, etc) you may use your action to force it to make a Constitution saving throw (DC 8+Int+Prof) or be immediately disabled/deactivated. The creature has disadvantage on this save if it is surprised.
Ok, I think player-character wise this project is almost there. After all the PHB wizard, druid, bard, etc can be pretty much used as-is. Plus there’s WotC’s Modern Magic Unearthed Arcana which gives a bunch more options (and was the inspiration behind this whole thing).
About hacking and similar rules, I suggest to contact Ceiling90 through Reddit:
https://www.reddit.com/user/Ceiling90
He designed some really interesting Sci Fi rules, includind rules for Hacking and warefare:
https://www.reddit.com/r/UnearthedArcana/comments/3c6fmf/pearl_of_dark_flow_v21x_updates/
I think you 2 together can build something really good.
I’ve noticed players who like sci-fi D&D 5e rules are too isolated on the net. When peaople are too isolated, ideas have difficulty to grow. It would be nice if people who like to design sci fi D&D 5e homebrew will join a little bit together.
I suggest also to contact DMwoodsy (who has mayde some kind stuff about sci fi in general, starships in specific):
https://www.reddit.com/r/UnearthedArcana/comments/3scw3p/wip_homebrew_scifi_scifi_players_handbook/
And, finally, I suggest to contact doctor necrotic (who is most known for his blog “Daemons & deathrays”:
https://www.reddit.com/r/UnearthedArcana/comments/360v7o/5e_sciencefantasy_racial_archetype_monster_and/
https://daemonsanddeathrays.wordpress.com/
More heads focused on sci fi rules, maybe will produce mor significant rules.
For now, your work is really good. 😉
LikeLike
Thanks! It’s always good to see what others are up to.
LikeLike